The Intelligence Brief Podcast: OSINT and its Application
Telegram Investigations, their Relevance in the Russia-Ukraine War and the Decentralised Web 3.0
OSINT expert Loránd Bodó shares a glimpse into the future of OSINT. Together with Anne-Lynn Dudenhöfer, our podcast host and analyst, he discusses the use of social media ecosystems by extremist networks, Telegram investigations in the context of the Russia-Ukraine war, and the Decentralised Web 3.0
Why has Telegram become – and will most likely remain – a critical source in the Russia-Ukraine war? Can blockchain technology benefit OSINT? What advantages or challenges does the decentralised web hold for future investigations?
The following article about Telegram investigations, their relevance in the Russia-Ukraine War, and Decentralised Web 3.0 has been created based on our first episode of the Intelligence Brief: OSINT and its application podcast. Listen below and to find more episodes, visit our podcast page.
In this episode, Anne-Lynn Dudenhöfer, Intel Desk Lead at HENSOLDT Analytics, spoke with Loránd Bodó, an OSINT expert and founder of OSINT Jobs. OSINT Jobs is a job portal dedicated to open positions in the field of open-source intelligence.
In the interview, Loránd shares his predictions on the future of open-source intelligence (OSINT) in the context of decentralised technologies, blockchain, and the Internet of Things (IoT). He also talks about the use of social media ecosystems by extremist networks, and Telegram investigations in the Russia-Ukraine war.
Table of Contents

About Loránd Bodó
Loránd Bodó is an OSINT expert and founder of OSINT Jobs. He works as an open-source intelligence consultant, and previously, was the open-source intelligence producer for NBC News.
He speaks English with German and Hungarian both being his native languages. He studied Arabic for three and a half years during his bachelor’s degree.
After completing his higher education entrance qualification, Bodó served in the German military for almost two years. Through which, he developed an interest in international politics and security.
He then went on to study Political Science and Oriental Studies with a focus in international terrorism. After obtaining his bachelor’s degree, Bodó went on to complete Master’s Degrees as well due to his passion for understanding better why people commit terrorist crimes.
Recent OSINT Trends: Tools & Investigation Methods
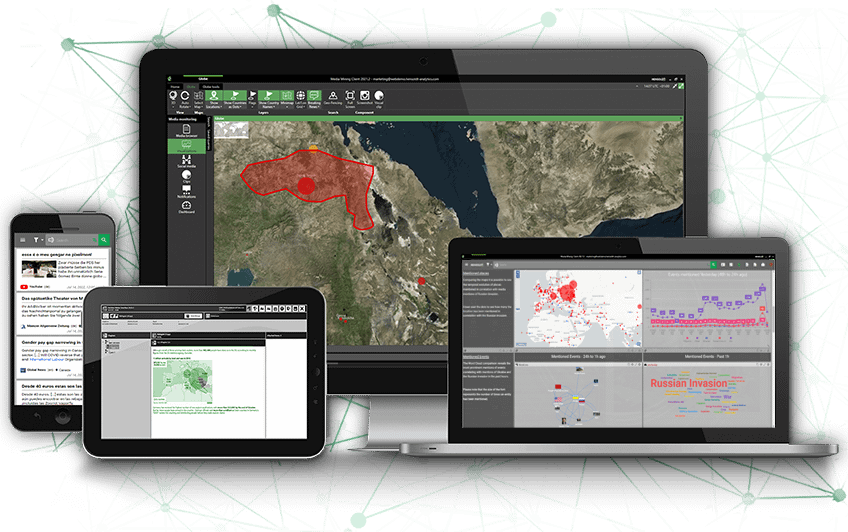
Open-source intelligence (OSINT) is a fast-paced intelligence method that has rapidly gained significance in the defence and security sector as well as the private sector over the past five to ten years.
Historically, OSINT has been around for decades, primarily in the form of translating news and radio broadcasts around the world. But around the mid-2000s, an explosion of information started when different methods of information sharing began overlapping.
- The availability of mobile phones and networks
- Social media apps that allow anyone to record and share information
In terms of recent trends, OSINT has become massive now. Over the past five years, it has grown exponentially, and with The Economist’s “The Promise of Open-Source Intelligence” in August 2021, everyone most likely knows about OSINT by now. If not everyone, then at least big organizations, executives, and those who read The Economist. The article showcases the power of OSINT, which leads to the following trends below.
Trend 1: Investigations in Russia-Ukraine War
With Russia’s invasion of Ukraine, there has been an explosion of an army of investigators or crowdsourced investigations. Established entities have been conducting these investigations for a long time, but now, especially on X (formerly Twitter), many other people come out of nowhere. They then start publishing analyses and sharing information, which makes it quite difficult for analysts. This is because analysts have to verify every finding.
This trend is projected to continue to grow, especially around established organizations that try and utilize these army of armchair investigators. Essentially, anyone with internet access, a desktop, and is passionate about doing something, can contribute to this mass information.
What we are observing right now in current Russia's invasion of Ukraine is the explosion of this army of investigators or crowdsourced investigations. You have established entities that have been doing this for a long time but you can also see and observe, especially on Twitter, many other people, who come out of nowhere and start publishing analyses and sharing information, which makes it quite difficult for analysts. Because you have to verify everything.
Loránd Bodó
Trend 2: The Transfer of Intelligence from Top Secret to Public
Recently, secret intelligence was shared for the first time in the UK, which is new. While intelligence is almost always something secret, the availability of open-source intelligence has created an era of information disorder. This means that when there is a lot of information coming from many sources, countries and parties can use this to their own advantage. Therefore, intelligence agencies must make sure that the information is trusted and verified so that it can’t be weaponized.
Trend 3: More and Better Artificial Intelligence Algorithms
Because so much information needs to be processed today, there is an increase in artificial intelligence (AI) algorithms and better AI-based algorithms. The amount of information will only continue to grow with the Internet of Things (IoT), which includes information in a way we can’t understand now, but when combined with data science techniques, could be understood in the future.
Currently, experts believe that the Internet of Things (IoT) is specifically under discussed along with combining AI technology and big data processing in open-source intelligence investigations.
Lastly, the amount of information is affected by blockchain technology, which leads to the question of how we could use this, especially in the age of mis- and disinformation.
It should also be noted that these advancements do not negate the need for one or more analysts.
Examples of Media and Messaging in Extremist Groups
One Platform Does Not Fit All
When talking about extremist groups or terrorist groups using technology or media messengers, we should think about it in terms of ecosystems and not that there is just one platform. This doesn’t mean that there are preferences, but to tackle terrorist use of the internet, one must investigate the entire ecosystem: hosting providers, tech infrastructure, and everything that comes with both areas.
Common channels include big social media platforms like YouTube, X (formerly Twitter), Facebook and so on, where these groups can then set up accounts or join conversations where they may find people who might be interested in what they have to say. Conversely, these big social media platforms have significantly ramped up their efforts to detect such content.
Telegram Use in Extremist Groups and Times of War
With the above being said, Telegram errs to be the preferred platform as it still used by many groups. Its popularity is widely attributed to user friendliness, which is incredibly important. Secondly, Telegram is often used because of its wide user base, which means more people can be reached. Finally, Telegram has a level of security that other platforms do not while also having a wide range of features, such as video and image sharing, call and so on.
However, Europol has cracked down significantly on some of these groups. One example is by doing internet referral action days where they work together with tech companies to do massive takedowns. The most successful result that specifically targeted so-called Islamic states and supporters on Telegram was in 2019. Experts in the field were talking about the results heavily on X (formerly Twitter) because they meant that researchers and everyone looking into these groups were targeted.
Telegram Use in the Russia-Ukraine War
Telegram was created in 2013 by Russian-born tech entrepreneur Pavel Durov. The messenger platform has a much larger user base in Russia than, for example, Facebook or X (formerly Twitter). According to a Deloitte study from 2021, 61 percent of polled Russians at the time were using Telegram. However, the platform is independent from the Russian government.
Currently, many major news outlets have been shut down in Russia and access to some social media networks, such as Facebook, have been blocked. Therefore, Telegram has become a critical source in the Russia-Ukraine war for both Ukrainian and Russian communication alike.
Both sides communicate about the ongoing conflict and share insights about troop movements, attacks, and even potential war crimes being committed. For governments, the defence and security sector, and journalists alike Telegram allows for a window into the war on the ground. And, if verifiable, there may even be a potential for such content to eventually serve as a basis for holding war criminals accountable.
The Critical Importance of Verification
There are great outlets, such as the Center for Information Resilience, that have been doing excellent work to verify information. For example, this map details everything that has to do with the invasion of Ukraine. Before something goes onto the map, they have a rigorous process of verification to make sure that nothing goes on it that shouldn't be on there.
When talking about the world of Telegram, once one channel
has been identified, more channels can usually be found. Then, the problem from
an analyst’s point of view is to make sense of this kind of messy data. Many topics
and similar themes pop up. The same people will make the same claims for
example, that “an advancement was spotted here in this area or artillery strike
in this area”. This information still needs to be verified.
Techniques for Using Telegram in OSINT Investigations
One common way of building up a database of intelligence is
to use search engines, such as Google, in combination with site operators to
find index content, for example, from X (formerly Twitter).
From there, on X (formerly Twitter), accounts link to Telegram
sources, and from there, similar links to other channels exist.
Gradually, a collection is built up. However, previously
stated, it is extremely challenging to verify the accuracy and veracity of this
kind of content. Furthermore, to verify who’s behind the channel because information
can be also shared for various purposes or reasons.
In the scope of the invasion of Ukraine, Bodó has created a list to help analysts
follow the invasion minute by minute. With the help of analysts and
experts, not only is X (formerly Twitter) content accessible but also Telegram
content. These people are content aggregators. They go on to Telegram and also
other sources, find the videos, and upload them on X (formerly Twitter).
While approaches like this help with monitoring, it is not
recommended for time-critical decisions.
Other Channels Being Used in Extremist Groups
When it comes to the wider far-right, Rocket.Chat and Discord are popular platforms. Furthermore, gaming platforms are very popular among these far-right communities, which are used to exploit the gamification element these platforms. Research institutes, such as the Royal United Services Institute (RUSI), are leading initiatives on the exploitation of gamification to understand how extremists are using gaming platforms or the concept of gaming in the context of radicalization.
Again, researchers cannot rely on just one platform to investigate but rather a cross-platform approach.
The Use of the Surface Web by Extremist Groups
A common misconception that many might have is that these extremist groups are operating on the Dark Web. However, the truth of the matter is that these groups are operating on the surface web as shown by the 2022 Report by Tech Against Terrorism. Through their research, they found 198 websites operated by terrorists and violent extremists—all accessible by everyday search engines. These websites promote ideologies such as neo-nazism, also Salafi jihadism, and incel ideology.
The report also dispels a common misconception that social media is the only platform that these extremist groups are using. In the Tech Against Terrorism report, not only were websites found that led to groups such as the so-called Islamic State, Atomwaffen Division, Combat 18, and the Taliban but data about monthly visits to these sites as well. The latter proves that the clear web is also a high-traffic platform for these groups.
An example was on Wikipedia, where the Islamic State’s page has content disparities based on language. In Arabic, there is additional content with more links. These links then lead to archiving services for all the content.
Similarities Between Right-Wing Extremists and Salafi Jihadist Groups
Firstly, as with all extremist groups, the ideology stands that the members belong to an in-group while the outgroup is an existential threat. Their similarities do not end there as these groups also tend to use similar platforms to spread their messaging.
As mentioned above, Telegram is a popular platform for these groups, and it is even believed that the group learn from each other through what is being reported in the news. This is seen through references on Telegram about it, such as messages that point out, “Hey, this is bad practice. Remember don’t do this.”
The two groups also share an emphasis on operational security with specialized groups that research and provide advice on how to stay under the radar, how to evade surveillance, etc.
What's also interesting between these two groups is the operational security that they both emphasize. On both sides, you can find specialized groups that research operational security and provide advice on how to stay under the radar, how to evade surveillance, etc.
Loránd Bodó
Differences Amongst Right-Wing Extremists and Salafi Jihadist Groups
One difference is that those on the far-right spectrum were one of the early adopters of cryptocurrencies, which implies that these members are then more focused on upcoming technologies and how they can be used. The motivation here belongs to decentralization or the idea that there’s a blockchain and no need for an intermediary or a government institution that controls everything. Essentially, one can send money back and forth securely.
Reports also show that Bitcoin has specifically been used by Salafi jihadists, such as the so-called Islamic State, to gather donations to finance terrorism. While these initiatives have been reported, the mechanism is not being used to a massive degree with millions of dollars, for example.
Web 3.0 and the Use of Decentralized Platforms
When talking about the internet as we know it today, we’re referencing Web 2.0, which means that online users share their thoughts with the world through pre-designed apps. Their activity is then tracked and/or stored in various ways by such applications and platforms.
Conversely, Web 3.0 applications are built on blockchains and decent decentralized networks of numerous peer-to-peer nodes. The term Web 3.0 was coined by one of the co-founders of Ethereum, Gavin Wood. The main takeaway is that content is not hosted on a central server. At the moment, large organizations, such as Google, have crawlers that scan and crawl the web and save the information. Whenever we use Google, we are not searching the web. What we are actually searching is a copy of what Google has from the web. Furthermore, they can show or decide which content we see.
In this context, Web 3.0 refers to decentralized apps that run on the blockchain. Currently, there are many organizations and startups that are trying to figure out what they could build and how Web 3.0 could work. From an OSINT point of view, the best practice in the meantime is to use different search engines. Each search engine has a different algorithm and archive for showing content.
Web 3.0 is also distinct from or different from what Tim Berners-Lee, inventor of the World Wide Web, refers to as “the Semantic Web”. The Semantic Web is about making the internet data machine-readable. This existence of the Semantic Web exists, for instance, when typing something into Google. For example, “where’s the nearest cafe”, and then Google understands the search intent and shows the information.
The problem we have is that as with any technology, it's a double-edged sword. You're going to have people; millions, billions of people using it for something good, making use of it. Then you have a few, who exploit it for whatever reason.
Loránd Bodó
When it comes to violent extremists and terrorists, the decentralized web or decentralized applications, like other platforms, can be exploited. With any technology, it’s constantly a double-edged sword. There will always be people—millions, billions of people using it for something good and making use of it. Then there will be a few who exploit it for whatever reason.
Does this mean that decentralization should be banned? No. When the decentralized web opens to a wider audience, there will not be much difference between what happens now with Web 2.0 and the decentralized version. The most interesting part happens in the backend, which most people won’t see, which is how the content is stored.
Advantages and Disadvantages of Web 3.0
As mentioned above, search engines currently have the power to decide which content they show users. Now, if a terrorist group operates on the clear web, a search engine can easily delete the group’s sites from their index. This means, they cannot be found in their search results.This is a monopoly, which many people argue social media platforms do not have.
Obviously, violent extremist and terrorist propaganda shouldn’t be online, but there are grey areas. Furthermore, there are areas where no one should have this type of power. This is where decentralization, or the concept of it, comes into play because the movement advocates that no one should have the ability to censor information or be able to remove it. So rather than putting it on one server or one entity having control over all the data, it gets distributed and decentralized.
If something happens to this central server or entity, the information is gone. For example, if Google loses all their servers, then no one could access Google. This is highly unlikely, but still possible. With the decentralized web, data is stored on different machines and more secure.
According to Europol, the problem with terrorist content on the decentralized web or its technology is that it cannot be taken down. There’s no possibility to email someone and say, “Could you please remove this from the network?”. Even if the person says yes, there are still thousands of other nodes. Technically, it’s not possible to even know who’s part of the nodes or reach out to someone because it’s not a company.
Therefore, this is the greatest disadvantage of the decentralized web: it’s impossible to remove content from decentralized web apps because it’s not stored on one single server by one entity that has control over it. It’s controlled by the entire network.
There are numerous examples of how certain entities and groups have already exploited it but not to a very high level. This is because, at the end of the day, this technology is still being developed. There are many projects, very interesting projects, but the decentralized web also has limitations. It shouldn’t scare anyone.
Other Services Used by Extremist Groups
Social Media and web aside, extremist groups also utilize other services, such as cloud services to host videos—one of the most popular being, but not limited to, Google Drive. The content uploaded to the platform then allows the groups to share and send links on platforms like Telegram.
InterPlanetary File System, a similar albeit decentralized service, is a peer-to-peer so-called hypermedia protocol designed to preserve and grow humanity’s knowledge. The way it is working is that you save a file in the system’s network, and you become part of a wider network. When someone tries to access that file or look it up, that person will ask in the network about this file and the system will point you to the nodes. When downloading the content, the user then automatically becomes another node and serves the downloaded content to another person.
This is pretty similar to the BitTorrent network. In order to download a torrent, one must also become a host at the same time, which creates this distributed network. This method makes it impossible to take this content down because it’s stored on thousands of machines rather than one single server.
The Future of Open-Source Intelligence Investigations
Crowd-Sourced Investigations
Today, it is a great advancement that one can follow a war minute by minute even though it is not the first time. This is largely because of the explosion of Telegram. Users upload videos from everywhere, which makes it challenging to document as well.
This expansion and complexity of documentation is the possible future of OSINT. Therefore, established organizations, such as bellingcat or Center for Information Resilience, will utilize this army of volunteers that often times dedicate hours and hours in their spare time to just document, geo-locate, verify, and add everything into a database. Due to the importance of the work, crowd-sourced investigations could take off, but also pose difficulties in terms of management of hundreds of people.
On one hand, more hands on deck is good. How long does it take one person to geo-locate? To first of all, collect relevant videos, then verify them including geo-location, analyse them, and then write everything up? How long will it take one analyst? But if you have hundreds, it’s a quick job but someone needs to also make sure everything is correct.
On the other hand, it can be also bad. It can go wrong, which can already be seen today. News organizations take a video and then retweet it and try to make some headlines with an mis- or unverified video. Then, people have to point out that this video is not from the current war in Ukraine but rather from Syria.
The Utilisation of Technology
For the future, combining data science and other technologies will also be incredibly helpful. Not only the combination but also the use of new technologies, ground-breaking technologies, such as blockchains, can change how investigations are done.
The idea is, for example, that there is a public ledger that keeps track of everything, and it’s impossible to change this. Therefore, we have the fundamental truth recorded on the blockchain.
Then, with crowd-sourced investigations, the blockchain can be utilized to make sure that whatever video gets documented is recorded in this blockchain. The blockchain will then identify that this video is not there yet, which means that this hasn’t been recorded yet. Ultimately confirming that the video is new or has been recorded, it’s from this conflict, etc.
Utilising this technology to counter mis- and disinformation might also be possible. There are most likely companies already thinking about how they could use this technology, especially in terms of incentivisation. There are some blockchains, such as Ethereum, where the incentive is a native token on that blockchain. When someone contributes, they also get a reward.
So those who geo-locate could get a token, and the more you geo-locate, the more tokens you can get. If the value of the tokens is, for example, a couple of hundred dollars, then maybe someone could make a living out of this as well while doing something good.
Methodologies and Technologies of Web 3.0
First of all, the future will focus on monitoring terrorist and extremist groups. Those companies and platforms that offer decentralised services are not bad. Rather, they can be exploited, which we need to be wary of.
From an OSINT point of view, identifying these kinds of services and understanding the group as a whole will be a priority. Not only this but to also understand where they operate online because obviously, they will have some sort of homepage or website where they interact with many people. These terrorist groups and extremists tend to want to be undetectable.
This is where Telegram can be useful. Once the kind of decentralised service is identified, it is easy to find out if the content from this platform is being shared. This can be done by looking at how the URL domain looks. From there, using the Telegram desktop client, it is possible to search within chats and channels to find the name of whatever technology is being used. No results mean that the information wasn’t shared… but that doesn’t mean that it doesn’t exist. For example, a search of “IPFS” shows links to guides and other types of content. This is how one would go about finding this kind of technology.
There are also other technologies that need to be download in order to participate in this kind of network. Then there are also the legal and ethical aspects, namely verification of the content. By downloading this technology, the user immediately acts as a node, which means he or she is also indirectly distributing such content. Is this ethical, is this legal? The answer to those questions will also be heavily scrutinized in the future.
Conclusion
To summarize, many platforms are currently being used by right-wing, extremist groups, but there seems to be a favour towards Telegram. Usually, as a first step these groups use web-based apps such as X (formerly Twitter), YouTube, and/or Facebook to attract followers. This is to reach more people as those platforms are more freely accessible to the public, and then they move to encrypted, or at least partially encrypted, apps such as Telegram. From there, other platforms, such as file sharing, are used to disseminate content.
Decentralised platforms are growing in popularity, but pose a specific risk. Without having a centralised server, content can live forever through its users and their nodes. With the wrong content, content meant to harm groups or individuals, dangerous messages and actions can spread quickly without any hope to delete. This doesn’t mean this technology should be stopped but rather more closely monitored in the future.