The digital landscape
continues to change faster than the technologies used for intelligence
gathering. The sheer amount of information generated daily poses a significant
challenge in terms of resources. Meanwhile, the rapid evolution of digital
communication platforms creates challenges of its own. Law enforcement
agencies, private companies, and security consultancies alike suffer from
shortage of personnel, time, and budget to run comprehensive investigations
that could match the scale of their task.
Luckily, open-source
intelligence (OSINT) tools grow more powerful with each passing day and month.
Even more luckily, many of these tools are free to the public. Below, you will
find our list of the 12 best free OSINT tools, which are specifically valuable
for person-of-interest investigations.
Table of Contents
A Brief History of Persons-of-Interest and OSINT Tools
Before we dive into the free OSINT tools below, it’s important to understand what exactly a person-of-interest is. Not only this but also how current investigations face challenges while using OSINT tools to identify POIs.
Person-of-Interest (POI) – Definition
Person-of-interest is a term originally widely used by law enforcement and intelligence officials to identify someone linked to and/or in possession of information pertinent to an ongoing criminal investigation. As the specialisation of online investigations grew beyond the military and law enforcement into private sectors, the term has been adopted by trained practitioners (for example cyber security experts or open-source intelligence analysts) conducting specialised investigations of persons. The term has no legal implications.
Nowadays, persons
suspected of illicit activities are tech-savvy and resourceful. They move
throughout the digital landscape with access to a much broader set of tools to
conceal their identity and activity online. As a result, it has become much
easier for persons-of-interest (POI) in investigations to slip under the radar
of law enforcement authorities, prosecutors, and even investigative
journalists. Those searching through open-source intelligence must be
particularly vigilant in exploring every angle. Furthermore, one important
aspect of POI investigations which can sway the conclusions of an OSINT report
is context.
Context Awareness in OSINT Investigations
Peter Cochrane, an international sought-after advisor and consultant with over 40 years of technology and operational experience, summarised the necessity for context awareness in interpreting intel on the topic of modern hybrid warfare:
“[…] intelligence systems have to be responsive to long-term monitoring and engage in deep observation and analysis of the situation. The data must be applied to the wider context to reveal unknowns and contingencies.”
This, suggests Cochrane, calls for minimization conditions that foster errors. For example, these could be focusing on narrow situation modelling or not factoring in human and machine cognitive bias.
Therefore, an efficient and conclusive strategy for OSINT investigations of POIs combines automated cross-media intelligence gathering workflows with open-source tools developed to target very specific information gaps.
The Intelligence Brief Podcast: OSINT and its Application
Telegram Investigations, their Relevance in the Russia-Ukraine War and the Decentralised Web 3.0
13 Free OSINT Tools for Persons-of-Interest Investigations
We asked our in-house OSINT analysts to share their favourite and freely available resources for performing a deep-dive investigations meant to uncover the digital footprint of POIs. The following open-source investigative tools are powerful but come with limitations. To get the most out of your investigation, we recommend using these tools alongside a media mining system. To learn more about The Media Mining System we have created here at HENSOLDT Analytics, read here.
BuiltWith Technology Lookup
BuiltWith covers 60,409+ internet technologies, which include analytics, advertising, hosting, CMS and many more. By entering a URL in the search bar, you can see the elements a website has been built with and what tools it uses. With BuiltWith.com Technology, data is accessible as far back as January 2000.
Have I Been Pwned
Have I Been Pwned enables investigators to quickly check whether their POI’s email address or phone number have been in any past data breaches.
Instant Street View
Instant Street View allows users to instantly fetch any address or place from the Google Street View. Users find the interface to be easier to navigate than attempting to do the same in Google Maps.
MapChecking
MapChecking helps you estimate and fact-check the maximum number of people standing in a given area. Set the parameter for the area you wish to measure, choose how populated it should be, and the tool will give you an estimate number of people.
Pushshift’s Reddit Search Application
According to the creator of the Reddit Search tool, this application allows for cross-post and comment searches, as well as specific user or subreddit searches. In addition, OSINT analysts can aggregate data to identify trends. As of 2022, reddit is blocked in India, Indonesia, Russia, and China.
Radio Garden
Radio Garden allows you to browse radio stations by rotating the 3D globe. It doesn’t map all existing stations, but it’s a helpful tool to add local reference sources to your report.
Snap Map
Snap Map ran by Snapchat aggregates a selection of public snapchat media uploaded by its users. The videos and images can be grouped by geolocation or public events.
Strava
Strava’s Global Heatmap focuses specifically on monitoring and visualising ‘heat’ made by aggregated, public activities over the last year. The public data shared by athletes from around the world identifies sport activity hotspots. The tool is also used by athletes to identify their next routes.
The Ventusky Web App
For those investigating events from all angles, weather conditions can play an important part in explaining the context of a POI’s movements. The Ventusky app provides interesting food for thought. The tool clearly displays meteorological data from around the world and allows users to monitor weather developments for any place on Earth at different times. Depending on data sources, some of the data visualisations date back decades.
The Wayback Machine
The Wayback Machine captures websites as they are and stores the screenshot, URL changes, and the timeline of changes for reference. The Wayback Machine is a crucial resource in the fight against disinformation as it records content meant to be short-lived.
TinEye
TinEye’s computer vision, image recognition and reverse image search matches your upload image with its duplicates online. It’s a useful tool for verifying users’ activity or connecting images to stock images databases.
Whois
Whois lists domain information allowing users to check the person owning the website you are looking at. The information provided to the Whois registry is voluntarily provided by the domain owners and unverified by the service.
Verify-Email.org
A useful email verification tool, Verify-Email connects to the mail server of an email address and checks whether the mailbox exists or not. This is particularly helpful for eliminating false lines of communications.
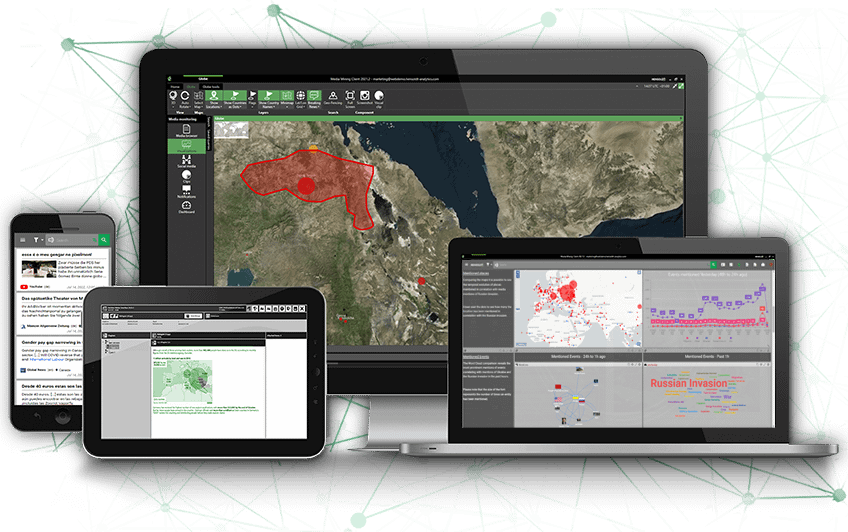
Configuring our Media Mining System
As mentioned above, free OSINT tools can only go so far. Using a proper tool as the basis for your investigation with the help of the free tools listed above will yield the best results.
The HENSOLDT Analytics system fuses a range of Neuronal Language Processing (NLP) and artificial intelligence (AI) together into one comprehensive platform. Our Media Mining System enables users to schedule and to automatically collect, index, systematise, and visualise open-source information from TV, radio, internet, RSS feeds, and social media 24/7.
The result is a robust, fully configurable platform able to extract actionable insights for situational awareness reports on very specific topics and events. Think of the Media Mining System as a wide net cast into the sea of information to pick out only the relevant pieces of intel – pieces that the system has been specifically calibrated to find.
Calibrating the Media Mining System’s Profiles
The Media Mining System comes with a prefabricated set of Profiles (or Named Entities, NE’s) covering persons, organizations and locations. These can be extended by end-users with proper permissions and training. Further classes of profiles, such as natural disasters, diseases or financial entities can easily be created using the profile-editor. Profiles form the basic building blocks for the complex construction of hierarchical interconnection, the Ontologies. Profiles capture the different ways an entity can be referred to in the real-world and across different languages simultaneously.
Please refer to the user guide for a step-by-step instructions in creating profiles. If you had not purchased the Media Mining System but you are interested in hearing more about it, contact us now to schedule a live demo with our team.
Once the Media Mining System identifies key profiles, hashtags, influencers and platforms for the searched query, the open-source intelligence analysts can generate a report summarising key findings.
Now, equipped with the first detailed analysis, the investigator will continue with their deep web search to gather additional open-source information for a complete person-of-interest report.